
Exploring the realm of Cloud Cybersecurity Solutions, this introduction delves into the crucial aspects of protecting data in today’s digital landscape. It highlights the significance of implementing robust security measures to combat evolving cyber threats, offering a comprehensive overview for businesses seeking to fortify their defenses.
This paragraph provides valuable insights into the types of solutions available, the benefits they bring, challenges faced during implementation, and the pivotal role of data analytics in enhancing security measures.
Overview of Cloud Cybersecurity Solutions
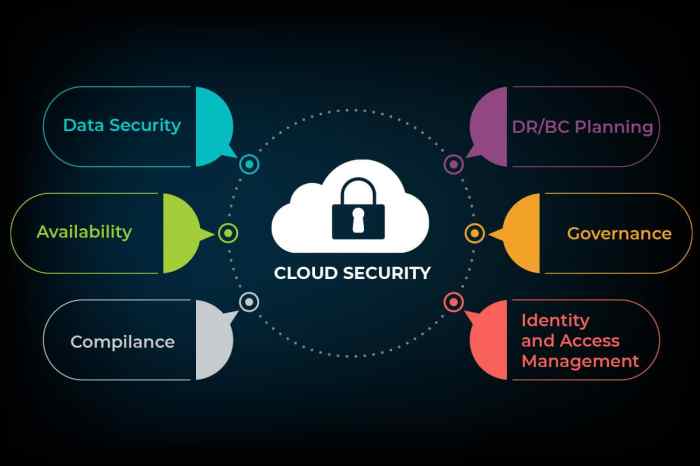
Cloud cybersecurity solutions refer to the set of tools, policies, and practices designed to protect data, applications, and infrastructure in cloud environments from cyber threats.
Implementing cloud cybersecurity solutions is crucial for businesses as more organizations are migrating their operations to the cloud. With the increasing volume of sensitive information stored in cloud servers, the risk of cyber attacks also rises, making it essential to have robust security measures in place.
Differences from Traditional Cybersecurity Measures
Cloud cybersecurity solutions differ from traditional cybersecurity measures in several ways:
- Scalability: Cloud security can scale more easily to meet the changing needs of a cloud environment compared to traditional security measures.
- Shared responsibility: In cloud environments, the responsibility for security is shared between the cloud service provider and the customer, requiring a different approach to security management.
- Visibility and control: Cloud security solutions provide enhanced visibility and control over data and applications, even in a distributed cloud environment.
- Automation: Cloud security solutions often incorporate automation to help detect and respond to threats more efficiently than traditional methods.
Types of Cloud Cybersecurity Solutions
Cloud cybersecurity solutions come in various types to address different security needs. Let’s explore the main types and their features.
Public Cloud Security Solutions
Public cloud security solutions are provided by third-party vendors and are accessible over the internet. They offer scalability and cost-effectiveness, making them ideal for small to medium-sized businesses. However, the shared nature of public clouds can raise concerns about data privacy and compliance.
Private Cloud Security Solutions
Private cloud security solutions are dedicated to a single organization and are hosted on-premises or by a third-party provider. They offer greater control and customization options, ensuring higher levels of security and compliance. However, private clouds can be more costly and require more resources to manage.
Hybrid Cloud Security Solutions
Hybrid cloud security solutions combine elements of both public and private clouds, allowing organizations to leverage the benefits of both. They offer flexibility, allowing businesses to store sensitive data on-premises while utilizing the scalability of the public cloud for other workloads. However, managing a hybrid cloud environment can be complex and require specialized expertise.
Role of Encryption in Cloud Cybersecurity Solutions
Encryption plays a crucial role in cloud cybersecurity solutions by securing data both at rest and in transit. It ensures that sensitive information is protected from unauthorized access, whether stored in the cloud or being transmitted between users and cloud servers. Strong encryption algorithms and key management practices are essential components of a robust cloud security strategy.
Benefits of Cloud Cybersecurity Solutions
Cloud cybersecurity solutions offer numerous advantages to organizations, enhancing data protection and contributing to regulatory compliance. By leveraging cloud-based security measures, companies can strengthen their defenses against cyber threats and safeguard sensitive information more effectively.
Enhanced Data Protection
- Cloud cybersecurity solutions provide advanced encryption techniques to secure data stored in the cloud, ensuring that only authorized users can access it.
- Regular data backups and disaster recovery services offered by cloud providers help organizations protect against data loss due to system failures, cyber attacks, or natural disasters.
- Cloud-based security tools can identify and mitigate security vulnerabilities in real-time, reducing the risk of data breaches and unauthorized access.
Contribution to Regulatory Compliance
- Cloud cybersecurity solutions enable organizations to comply with industry-specific regulations and data protection laws by implementing robust security measures and access controls.
- By centralizing security management in the cloud, companies can streamline compliance processes and demonstrate adherence to regulatory requirements through audit trails and reporting functionalities.
- Cloud providers often offer compliance certifications and attestations, helping organizations validate their security practices and meet regulatory standards.
Challenges in Implementing Cloud Cybersecurity Solutions

Implementing cloud cybersecurity solutions comes with its own set of challenges that businesses need to address in order to ensure the security of their data and systems. One of the main challenges is the complexity of managing security in a cloud environment, as it requires specialized knowledge and expertise. Additionally, businesses may face resistance from employees who are not familiar with cloud security practices.
Risks Associated with Cloud Cybersecurity Solutions
- One of the risks associated with cloud cybersecurity solutions is the potential for data breaches or leaks due to misconfigurations or vulnerabilities in the cloud environment.
- Another risk is the lack of control over security measures, as businesses rely on cloud service providers to implement and maintain security protocols.
- Cloud cybersecurity solutions may also be susceptible to distributed denial-of-service (DDoS) attacks, which can disrupt services and compromise data.
Strategies for Overcoming Obstacles in the Adoption of Cloud Cybersecurity Solutions
- Provide comprehensive training to employees on cloud security best practices to increase awareness and ensure compliance with security policies.
- Regularly assess and update security measures to address new threats and vulnerabilities in the cloud environment.
- Implement multi-factor authentication and encryption to enhance data protection and prevent unauthorized access to sensitive information.
Relationship Between Cloud Cybersecurity Solutions and Data Analytics
Data analytics plays a crucial role in enhancing the effectiveness of cloud cybersecurity solutions. By leveraging advanced analytics tools, organizations can gain valuable insights into potential threats, identify patterns of suspicious behavior, and proactively mitigate security risks. The intersection of cloud cybersecurity solutions and data analytics allows for a more proactive and adaptive approach to cybersecurity, enabling organizations to stay ahead of evolving threats.
Enhancing Threat Detection
- Data analytics tools can analyze vast amounts of data in real-time to detect anomalies and unusual patterns that may indicate a security breach.
- By correlating data from multiple sources, such as network logs, user behavior, and application activity, organizations can identify potential threats more accurately.
- Machine learning algorithms can continuously learn from new data to improve threat detection capabilities and adapt to emerging cybersecurity challenges.
Improving Incident Response
- Data analytics can help organizations prioritize and respond to security incidents more effectively by providing insights into the severity and impact of a breach.
- By automating incident response processes based on predefined rules and analytics-driven insights, organizations can reduce response times and minimize the impact of security incidents.
- Real-time monitoring and analysis of security events enable quick identification of security incidents, allowing organizations to take immediate action to contain and mitigate threats.
Role of Artificial Intelligence
- Artificial intelligence (AI) technologies, such as machine learning and natural language processing, can enhance cloud cybersecurity solutions by enabling predictive analytics and intelligent threat detection.
- AI-powered security tools can analyze massive datasets to identify potential security risks, predict future attacks, and automate response actions to mitigate threats in real-time.
- By continuously learning from new data and adapting to evolving threats, AI-driven cybersecurity solutions can provide more robust protection against sophisticated cyber threats.
Wrapping up our discussion on Cloud Cybersecurity Solutions, it’s evident that safeguarding data in the cloud is paramount for organizations in an increasingly interconnected world. By understanding the diverse solutions, benefits, challenges, and the synergy with data analytics, businesses can proactively protect their valuable information assets.
FAQ Compilation
How do cloud cybersecurity solutions differ from traditional security measures?
Cloud cybersecurity solutions focus on protecting data stored in the cloud, offering scalable and flexible security options compared to traditional on-premise solutions.
What are the key benefits of implementing cloud cybersecurity solutions?
Cloud cybersecurity solutions provide enhanced data protection, regulatory compliance, and scalability for businesses operating in the digital landscape.
What challenges are commonly faced when implementing cloud cybersecurity solutions?
Businesses often encounter issues with data privacy, compliance regulations, and the complexity of integrating cloud security measures into existing infrastructures.







